Guide To Securing Non-Profit Security Grants

Hardening Security For Non-Profit Organizations
When it comes to security, it's natural for non-profit organizations to ask: are we doing enough to keep people safe? The news is often full of alarming stories about the violence that creates fear and unfortunately, a lot of misinformation. It's important for schools, faith-based organizations, and other non-profits to make data-driven decisions and avoid alarmist attitudes that can take their security plans in the wrong direction.
Still, non-profit entities have faced security threats in recent years including:
- Cybercrimes
- Hate crimes
- Targeted violence
- Indirect threats
- Active shooter events
Protecting people in places that are typically open environments poses a unique challenge. Security experts must take a layered approach that integrates physical features with training and technology to create safer, more prepared buildings – while still making people feel as though they are in a warm, welcoming place.
Finding the money needed to make thoughtful security improvements is a big challenge for non-profits. But many are offsetting their costs by seeking out and applying for security grant funding.
FUNDING SECURITY IMPROVEMENTS WITH GRANTS
Grants are non-repayable funds, meant for specific activities as outlined in the applicant's grant submission proposal, awarded by federal, state and/or private agencies to non-profit organizations, schools and religious entities.
The grant process can be quite hard to navigate - and researching, applying for and managing grants is time-consuming work. Grant proposals require a team of people, including a project lead, a writer, and in the case of security grants, a security expert(s) to execute.
Grants supply funding for specific types of activity and are usually offered just once a year. This means that applying for grants is time-sensitive and extremely competitive. Your organization may be competing with hundreds or thousands of other applicants for a single grant.
It's not unusual for some federal grant programs to receive upwards of 25,000 applications
With grants, the federal agency providing the funding is more of an oversight committee -monitoring the project. In a cooperative agreement, the federal agency works alongside your organization to perform tasks within your project. The degree to which they work with you and on what, varies by program and agency.
Grants vs. Cooperative Agreements
One more thing to note as you move forward with your research and preparation is the difference between grants and cooperative agreements. They are nearly the same, but with one noted distinction.
According to Grants.gov:
"A cooperative agreement is distinguished from a grant in that it provides for substantial involvement between the Federal awarding agency or pass-through entity and the non-Federal entity in carrying out the activity contemplated by the Federal award.”
With grants, the federal agency providing the funding is more of an oversight committee -monitoring the project. In a cooperative agreement, the federal agency works alongside your organization to perform tasks within your project. The degree to which they work with you and on what, varies by program and agency.
A cooperative agreement is distinguished from a grant in that it provides for substantial involvement between the Federal awarding agency or pass-through entity and the non-Federal entity in carrying out the activity contemplated by the Federal award.
With grants, the federal agency providing the funding is more of an oversight committee -monitoring the project. In a cooperative agreement, the federal agency works alongside your organization to perform tasks within your project. The degree to which they work with you and on what, varies by program and agency.

25 GRANT WRITING TERMS YOU NEED TO KNOW
To successfully apply for and win a security grant, you'll need to know this basic terminology.
1. Budget period
Period of time in which your grant funds are available.
2. Block Grant
A grant awarded by a state or federal government agency that funds a specific need.
3. Capital support
Funds provided for endowment purposes, buildings, construction, or equipment.
4. Cost sharing
When you invest money into your organization's own project.
5. Direct costs
The total amount necessary to fund your project, which includes only the direct costs.
6. Disallowed costs
Charges that the grantor has determined are outside of the scope of the grant or are excessive or otherwise unallowable.
7. DUNS Number
The Dun and Bradstreet Data Universal Numbering System number, or "DUNS," is a nine-digit figure given to applicants to be used as an identifier. Frequently required for federal grants.
8. Equipment
Any item having an approximate unit value in excess of $500 and an estimated usefulness of more than two years.
9. Evaluation
A quantitative assessment of your project; a comparison of your original objectives and the actual project outcomes.
10. Letter of inquiry/Letter of Intent (LOI)
A brief letter outlining your organization's activities and its request for funding that is sent to an agency to determine if it's appropriate to submit a full grant proposal.
11. Letter of support
A simple letter attached as an addendum to your proposal. This letter should be from an "expert" or supporter of your project who tells why he/she believes that your project should be funded.
12. Multi-year budget
Budget representing the cost of a project of more than one year's duration; a separate budget is prepared for each year, with a budget summary presented preferably at the beginning of the budget pages; See alsoMulti-Year Funding.
13. Need statement
The part of the grant in which you explain, using both qualitative and quantitative data, why you deserve funding.
14. Operating foundation
A 501(c)3 organization classified by the IRS as a private foundation whose primary purpose is to conduct research, social welfare, or other programs determined by its governing body or establishment charter. An operating foundation may make grants, but the amount of grants awarded generally is small relative to the funds used for the foundation's own programs. See also 501(c)3.
15. Operating support grant
16. Organization budget
All funds budgeted for an organization's operations, activities, programs, and services during a fiscal year. Operating funds do not include capital funds, endowment funds, reserve funds or any other funds not allocated to the annual operating cycle of the organization.
17. Program income
The gross income earned by your organization that is generated directly by a grant-supported activity or earned as a result of the grant. It includes, but is not limited to: income from fees for services performed, the use or rental of real or personal property acquired under the grant, the sale of commodities or items developed or fabricated under the grant.
18. Project director
Person responsible for activities involved in the grant, including the evaluation and follow-up (also called "Coordinator").
19. Project cost
Total allowable costs incurred under a Federal award and all required cost-sharing and voluntarily committed cost-sharing, including third-party contributions.
20. SAM number
Also known as a Commercial and Government Entity (CAGE) Code, this number is a five-character identifier for your business that is required when applying for a federal grant.
21. Summary
An overview of your project that answers key questions such as: who, what, when, where, why and how.
22. Sustainability
A measure of how your project will continue when funding ends.
23. Site visit
Team of evaluators from the grantor agency evaluates your location and facilities. May include a review of your project plan and objectives with key personnel.
24. Three-column budget
A budget that shows three sources for funding: the grant maker (agency or foundation), outside funding (matching funds from a supporter), and your own in-kind support.
25. Third-party in-kind contributions
The value of non-cash contributions (i.e., property or services) that:
- Benefit a federally assisted project or program; and
- Are contributed by non-federal third parties, without charge, to a non-federal entity under a federal award
20 Physical Security Terms You Need To Know
Before you seek funding, you'll need to get familiar with the different types of security features out there.
While some of these items may conjure up images of an institutional-like atmosphere, know that manufacturers have made great strides in blending safety and aesthetics. Specifically, bulletproof barriers have come a long way in terms of design and appearance.
Wondering what level of ballistic glazing protection you need for your facility? While resistance ratings extend to UL Level 8, most bank barriers use UL Level 1 to Level 3 bullet proof glass. Learn more about the eight levels of bullet resistance and what bulletproof glazing option is right for you.
1. Access Card Readers
 Access Card Readers scan badges or ID cards, granting your employees access through a control point, typically a locked door. Card readers can scan bar codes, magnetic strips, smart cards and biometrics.
Access Card Readers scan badges or ID cards, granting your employees access through a control point, typically a locked door. Card readers can scan bar codes, magnetic strips, smart cards and biometrics.
2. Biometric Access Control
 Biometric Access Control systems scan an employee’s fingerprint, retina, or face (biometrics) and compare the results against previously stored data. If the data matches, the employee gains access through a control point.
Biometric Access Control systems scan an employee’s fingerprint, retina, or face (biometrics) and compare the results against previously stored data. If the data matches, the employee gains access through a control point.
3. Bollards
 Bollards, steel or concrete security barriers, protect your property and pedestrians from vehicle-ramming incidents. Manufacturers offer a variety of finishes and shapes to blend in with surrounding architecture.
Bollards, steel or concrete security barriers, protect your property and pedestrians from vehicle-ramming incidents. Manufacturers offer a variety of finishes and shapes to blend in with surrounding architecture.
4. Bulletproof Barrier Systems
 Bulletproof Barrier Systems offer UL-rated ballistic protection. They typically comprise bullet-resistant glass, doors, frames, countertops and other accessories to allow for safe, easy interactions with customers and visitors.
Bulletproof Barrier Systems offer UL-rated ballistic protection. They typically comprise bullet-resistant glass, doors, frames, countertops and other accessories to allow for safe, easy interactions with customers and visitors.
5. Emergency Call Boxes
6. Emergency Public Address Systems
 Emergency Public Address Systems allow you to broadcast emergency information throughout a building and/or outdoor space. They’re often used in conjunction with intercom systems for effective two-way communication.
Emergency Public Address Systems allow you to broadcast emergency information throughout a building and/or outdoor space. They’re often used in conjunction with intercom systems for effective two-way communication.
7. Fencing
8. Fire Alarm Systems
9. Lighting
10. Locking Devices
11. Mantraps
 Mantraps are small rooms, or vestibules, with two doors designed to “trap” your visitors before they are cleared to enter a secure location, either by a security guard or card reader system. Similar sally port systems are often used in prisons.
Mantraps are small rooms, or vestibules, with two doors designed to “trap” your visitors before they are cleared to enter a secure location, either by a security guard or card reader system. Similar sally port systems are often used in prisons.
12. Metal Detectors
 Metal Detectors screen your visitors at access points to find concealed metal weapons, including knives and firearms. You can purchase stationary walk-through models or portable systems, which conduct random screenings in any building location.
Metal Detectors screen your visitors at access points to find concealed metal weapons, including knives and firearms. You can purchase stationary walk-through models or portable systems, which conduct random screenings in any building location.
13. Security Alarm Systems
14. Security Guards
15. Shelters in Place
 Shelters in Place, once used primarily for tornado protection, are now built with ballistic steel to protect against shootings and explosives. Secured to your building’s foundation, they vary in size and can easily fit in a meeting room or classroom.
Shelters in Place, once used primarily for tornado protection, are now built with ballistic steel to protect against shootings and explosives. Secured to your building’s foundation, they vary in size and can easily fit in a meeting room or classroom.
16. Storage Safes
17. Training
 Training and Employee Awareness Programs are essential to effective security planning. Regular fire and weather emergency drills, as well as active shooter response training, help prepare your employees in the event of a real emergency.
Training and Employee Awareness Programs are essential to effective security planning. Regular fire and weather emergency drills, as well as active shooter response training, help prepare your employees in the event of a real emergency.
18. Video Surveillance Systems
 Video Surveillance Systems help deter and identify criminal activity. They’re usually positioned at entrance points and areas where you interact with visitors or customers. Their effectiveness depends on the number and location of cameras, and how often they are monitored.
Video Surveillance Systems help deter and identify criminal activity. They’re usually positioned at entrance points and areas where you interact with visitors or customers. Their effectiveness depends on the number and location of cameras, and how often they are monitored.
19. Visitor Management Systems
 Visitor Management Systems track people entering and leaving a building. The technology allows you to screen and monitor visitors using ID scanners, image capturing, electronic signatures and more.
Visitor Management Systems track people entering and leaving a building. The technology allows you to screen and monitor visitors using ID scanners, image capturing, electronic signatures and more.
20. Window Security Film
 Window Security Film, applied to your existing windows, can boost your facility’s forced-entry and blast security. It makes windows more difficult to break, offers shatter resistance and provides UV protection.
Window Security Film, applied to your existing windows, can boost your facility’s forced-entry and blast security. It makes windows more difficult to break, offers shatter resistance and provides UV protection.

What is CPTED And How Does It Affect Security?
Another term and concept you'll need to know is CPTED. Crime Prevention through Environmental Design (CPTED) is a design philosophy that emerged in the 1960s and 1970s, and has gained increased traction with school administrators and designers over the last decade. CPTED primarily provides unobtrusive deterrence through:
- natural surveillance: windows and sight lines make it clear to visitors that they are highly visible
- natural access control: a single point of entry welcomes guests while making potential attackers feel confined
- natural territorial reinforcement: landscaping clearly communicates the building’s presence and role in the community
Total Security Solutions has long advocated for this sort of comprehensive security, particularly in the areas of natural surveillance and natural access control. Security design specialists at Total Security Solutions can help administrators make informed decisions about what bullet-resistant products are suitable for specific uses, and how these can be deployed to enhance security without straining the educational environment.
Grant Application Timeline
Grants have three stages:
- Pre-Award
- Award
- Post-Award
You'll want to familiarize yourself with the specific tasks you'll need to perform at each stage. Download our free Non-Profit Security Grant Timeline to get a to-do list for each stage of your grant.
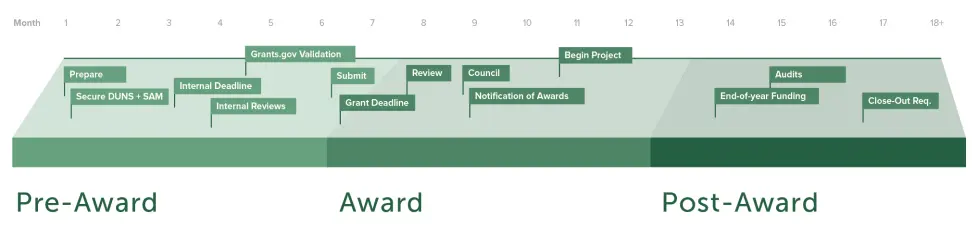
Pre-Award Stage
For the applicants, the Pre-Award stage is about research, information gathering and getting organized. It's best to get an early start on this phase in order to meet your application deadlines. You'll want to thoroughly understand the RFP as a first step. The RFP or Request for Proposal will outline the requirements for the grant submission including:
- Award limitations
- Important dates and contact info
- Formatting
- Scoring criteria
- and much more
This stage is the heavy-lifting stage for both the applicants and the agencies offering the grants. For the grantor, this time includes announcing their grants, pre-screening applicants and then collecting and reviewing the applications.
Be clear in your "need" for the safety/security items you are proposing to add to your building. Ask for products that are either missing or identified as high priority from your safety/vulnerability assessment (ie. if you already have video cameras, don't ask for more cameras, when your reception area does not have a barrier).
Many states require that you are actively engaging your County Emergency Manager (EM). If you have not been updating your County EM, you may not be eligible to apply for State or Federal Grants. As a good first step, add your EM to the distribution list for all of your required Fire, Lockdown and Weather related drills. Once each drill is completed, send a summary report to your County EM. The next step is to review your school safety plan with the EM, and make sure that it is signed off by the EM as well as your local law enforcement official (Sheriff or Chief of Police).
If you don't already have one, get your DUNS number early. They are required for most federal grants and can take weeks to obtain.
Award Stage
In the Award Stage, the workload is still fairly significant for the grantor, which has to evaluate hundreds, sometimes thousands, of applications. During this stage, the grantors select organizations to receive grants, and notifies them of their awards. Once the organizations have been notified, the grantor will develop a legal framework for disbursement of funds to the recipients.
Once awarded, you'll have to share your project's intended start date, completion date, and any major milestones, and provide a detailed, line item budget to your grantor.
Post-Award Stage
The Post-Award Stage is focused on evaluation, compliance, and project success. The grantor may conduct an on-site visit to audit your progress and usage of your funding. Your project will finish with a close-out process that includes reviewing all final reports.
Be prepared for audits, which are an expected part of most federal grants and required if the grant awarded is over $750,000.
Applying For The Grant
Applying for a grant to upgrade security for your school, synagogue, church, or non-profit entity means writing a compelling application that makes a clear case for your needs, based on data and an expert assessment. Your submission should include specific details about your goals and challenges and strategic, thoughtful plans for how you plan to utilize the funds.
Research: What Grants Exist?
There are many grants available for hardening security. It's important to look at what type of grants exist, and who is funding them.
Grants can be funded by federal or state agencies, or private entities. A simple search for security grants for non-profits will yield thousands of options.
One of the biggest sources of grant funding for schools, specifically, is the STOP School Violence Act, enacted in 2018. In it, Congress authorized nearly $1 billion in school safety and security grant funding to be spread out over the next ten years. About one third of it is targeted specifically at school security equipment and technology. The other two thirds is designated for prevention training and reporting technology.

Ten Tips for Successful School Safety Grant Applications
- Read grant requirements carefully to verify that you are asking for funding for enhancements that are authorized by the program.
- Demonstrate your school or district’s commitment to safety by describing substantive enhancements you have already implemented without grant funding.
- Demonstrate that the enhancements you seek funding for were determined by a valid assessment process. Using the results from an assessment that was conducted before a grant program was announced can carry a lot of weight with grant reviewers.
- Whether you conduct an internal assessment or involve an outside firm or government agency, involving local and state public safety officials in the assessment process can add credibility.
- Back up your requests with credible data. Avoid the use of the common alarmist and inaccurate statistics which can hurt your credibility. If the data is frightening (“X study shows that there is an epidemic of school shootings since X date”), it is most likely derived with bad methodology or involves a mischaracterization of good data.
- In contrast to the inaccurate and alarmist data that is prevalent in the media, on social media, and on the web, use solid and credible internal data to show how past successes with school safety efforts have been achieved.
- When possible, emphasize how you will use evidence-based or research-based approaches like Crime Prevention Through Environmental Design (CPTED) in your efforts to enhance school security.
- When possible, demonstrate how you will use other funding, no-cost measures, and collaboration with community partners to support and round out the enhancements you seek funding for.
- Have your “wish list” of things you know you need but cannot obtain funding for written down and ready to go. Being ready for the next grant program can help you define what you need, why you need it, and how you will implement it, thereby improving the quality of your application and speeding up the grant writing process.
- Deliver more than you promise when you are awarded a grant.
Grant Application Case Study
For an example of what we mean by number ten, consider the following case study:
Buncombe County Schools in North Carolina was awarded a $250,000 Readiness and Emergency Management for Schools Grant from the United States Department of Education. The district far exceeded the training goals listed in the grant application and allowed guest students from more than 40 school districts and non-public schools from across the state and Tennessee to attend grant-funded training sessions.
The district then re-applied for the grant the following year and partnered with several other districts in the region who had sent personnel to the training. The participating districts were awarded an additional $750,000 because Buncombe County Schools had proven that they did more than they had promised with the federal dollars they had been awarded.
Dorn reminds applicants: "The best grant programs are often highly competitive. Defining needs using a formal assessment process, being ready for the next program, matching requests to authorized expenditures and delivering more than promised can result in awards of multiple grants to make your students and staff even safer."

Write To Win
Some of the other keys that we have found to writing a winning security grant proposal include:
Being Specific
The more specific you can be, the better the grantor can understand that you'll be putting funding to good use. You need to clearly identify gaps in your current security, outline your security objectives and provide a list of specific security equipment, features, and protocols that you'll need to meet your objectives.
Speaking The Language
It's important to understand grant terminology and safety terminology so you can speak a common language with the funding agency.
Knowing What They're Looking For
Often brand-new grant applicants are so focused on asking for what they need, that they forget about the needs of the grantor. Ask yourself: what is our funding source trying to accomplish by offering this grant, and how can we make our need fit their priorities? Clues to answer this question can be found in the RFP.
Look at past awards given by that agency and see how much was awarded and for what.
It will be critical to be specific about what you'll be using your funding for and how much those items will cost. Get estimates from industry experts and vendors on these costs. Having real-world numbers will show accountability and commitment on your end.
8 Steps To A Comprehensive School Safety Plan
It's always good to confirm that you're taking the right approach and if possible, get insights from experts that will help you secure your grants.
One piece of advice that you'll find across various sources is to develop a clear school safety plan and include it in your proposal.
Here are the eight steps to a comprehensive school safety plan, as outlined by the U.S. Secret Service:

Establish a threat assessment team.

Create a list of behaviors that are not allowed and if witnessed, require intervention.

Develop and train personnel to use a central reporting system.

Consider when law enforcement shouldbe called to intercede.

Create your threat assessment procedures.

Develop your list of risk management options.

Promote safe school climate initiatives that respect mental health, difficulties, and differences.

Provide training for personnel on the steps outlined above.
Other types of non-profit organizations can model their safety plans based on this one, and include specifics that make sense for them.
Don't Forget About Safety Assessments/School Safety Audits
Many grants have specific requirements for safety assessments to be done prior to your application. Some grants require schools to use their specific state's assessment tool. Make sure to double-check the requirements on your grant.
Grant Help: Hiring Proposal Writers
Many non-profits are strapped for time and staff for daily operational tasks. They often don't have the bandwidth to tackle the time-consuming grant proposal writing process. While it's tempting to shop around for someone who can take this off your plate, it's important to know that a well-written proposal is not a straight ticket to grant funding. It's also important to consider the extra costs of hiring a professional.
If you do decide to hire a professional proposal writer make sure they:
- Can provide references/proof of success from prior clients
- Can meet your application deadlines
- Specialize in the type of grant you're applying for
Grant Tracking: What's The Status?
It's important to stay organized, especially when juggling multiple applications for multiple grants. Some people love spreadsheets, while others use grant management software or even Trello boards. Whatever method you choose, make sure to update it regularly and keep in touch with grantors to check the status of your applications.
10 Common Mistakes To Avoid When Applying for Grants
We've covered best practices, but what about the pitfalls to avoid when applying for grants? Here are ten commonly made mistakes.
- Appealing To The Wrong Audience - This means asking the wrong people for money for the wrong thing.
- Missing or Incomplete Questions - This is 101! Proofread, proofread, proofread, and don't forget attachments.
- Objectives Are Not Specific or Measurable - Have a clear purpose and figure out how you'd demonstrate success.
- Costs for Budget Are Not Substantiated or Inflated - Double check your numbers. Don't pad.
- Your Proposal Is Poorly Written - Your proposal needs to follow a logical framework. It also needs to follow the order outlined by the grantor.
- You Didn't Make A Compelling Case - Write with your head and your heart.
- Waiting Until The Last Minute - Start your process early and allow enough time to follow the steps above. Don't rush!
- Limiting Yourself - There are many types of grants out there to apply for including state, federal, private. Do your homework!
- You Didn't Customize/Personalize - Make you sure you consider your audience and tailor your submission to them.
- Being Deceitful - Don't say or promise anything that you cannot back up later during audits, on-site visits, etc.